In this blog, I will show you how I personally do anonymous browsing and how you can hide yourself on the internet like real hackers.
We will start from the basics like what is Tor, what is tor browser, how to use tor browser, with its purpose, properties, advantage, installation on both Linux and Window also I have shared some configuration of the tor browser that I used to make my browser more secure with some safety points.
So Let's get started...
- What is Tor?
- What is Tor Browser?
- Tor Browser Download
- How to Install Tor Browser in Linux?
- How to Install Tor Browser in Windows?
- How to Use Tor Browser?
- How Does Tor Work?
- How to Safely Use Tor Browser?
- Things You Should Know Before Using Tor Browser
- Is Tor Browser Safe?

What is Tor?
Tor (The Onion Router) is free open-source software or service that enables you to browse the internet by hiding your real identity. You can run Tor as a browser on your computer/Laptop and also you can run Tor Service as a command line. It mainly enables a way of anonymous internet surfing.
What is Tor Browser?
Tor Browser is a web browser that is not normally used like other browsers such as Google Chrome, Mozilla Firefox, Internet Explorer etc. Tor browser is specially designed for anonymous surfing, it stops others to track your activities by providing different identity.
Tor originally designed by the United States Navy to protect sensitive U.S. government communications. But It is now a free open source, browser that is available to the public and still, its usage continues by the government.
However, Tor always linked with the darknet and criminals but officials like law enforcement officials, security reporters, activists, security professionals, ethical hackers, ordinary security-conscious individuals and other security field related people often use the browser for legal purposes.
Tor Browser Download
As I discussed the Tor project is free and open for the public so you can easily download and use it. Tor is available for Windows, Mac, Linux and Android, you can directly download it from the official website by clicking on Tor Browser Download, then choose according to your system. Check the below image for the reference

How to Install Tor Browser in Linux?
Let's see how to install the Tor browser in Linux. Below I have installed Tor browser in Kali Linux the process is the same for other Linux distribution such as Ubuntu, CentOS etc.
I use Kali Linux because it is specially designed for hacking purposes if you also want to know what is Kali Linux and How to install then click on how to install Kali Linux
Installing Tor Browser is very simple and quick to follow the below-mentioned steps to see the process:
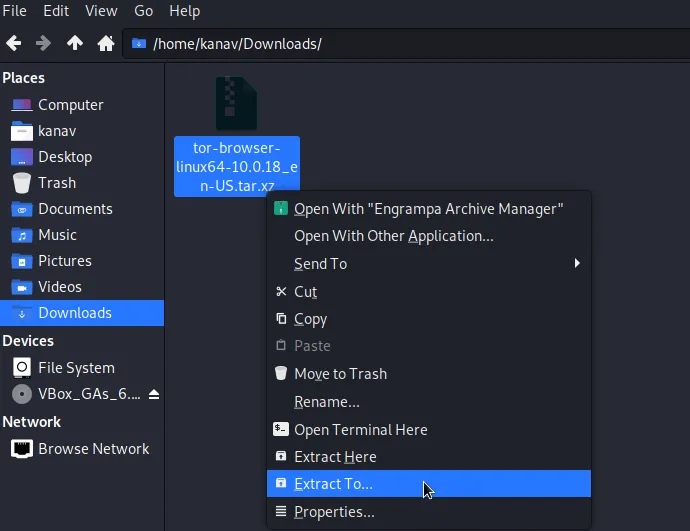
Step 1: After downloading Tor Browser you need to go to the download location and extract the downloaded file. So right-click on your downloaded file that will look like "tor-browser-linux64-10.0.18_en-US.tar.xz" and click on Extract Here.
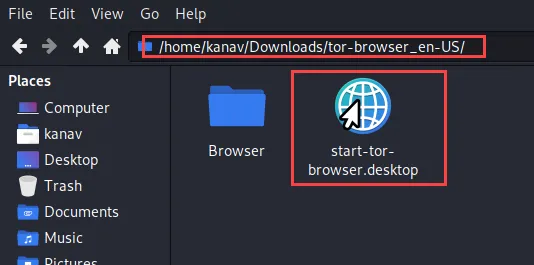
Step 2: Now go inside the extracted folder and double click on start-tor-browser.desktop file
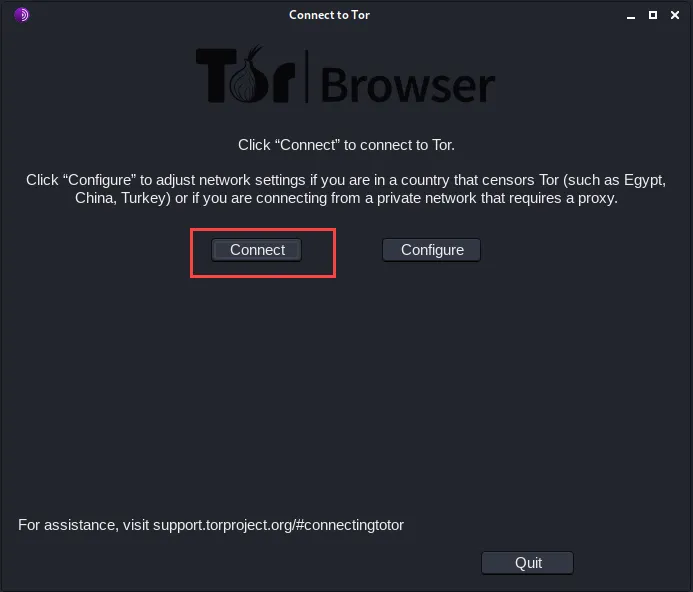
Step 3: Now you will see your Tor browser will be launched and asking for you to Connect or Configure. For now, just click on Connect we will configure it later.
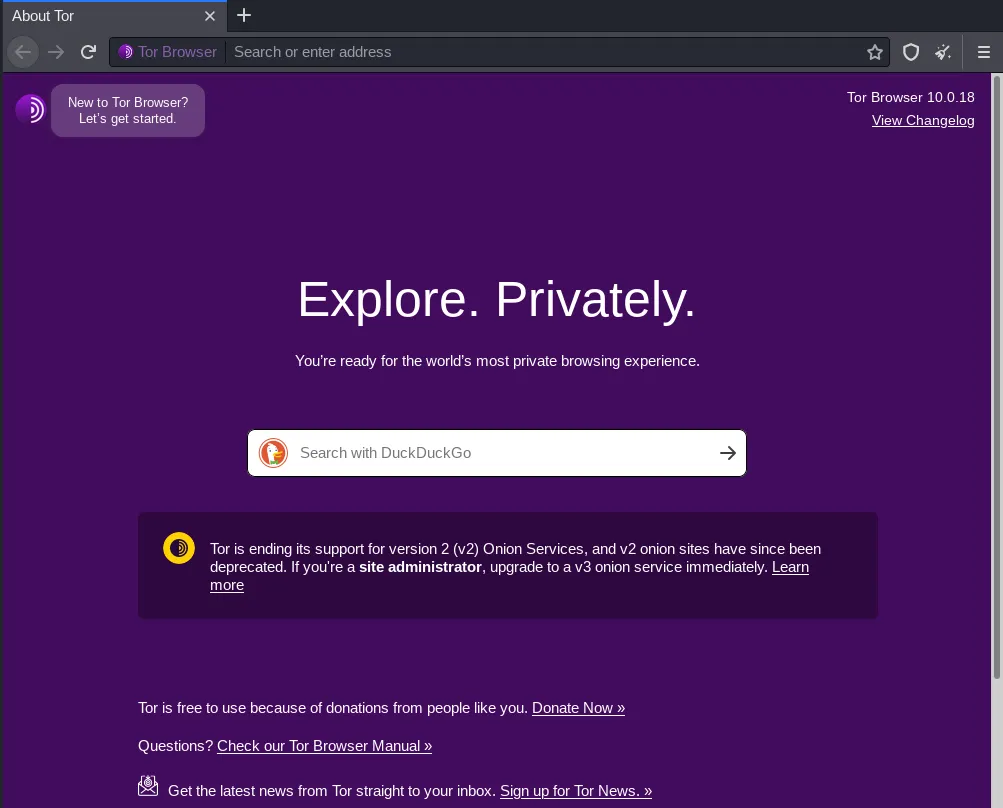
Step 4: Now within few seconds it will connect you with the Tor network and you will see the Tor browser screen from where you can start your anonymous browsing.
How to Install Tor Browser in Windows?
Installing Tor on Windows is much easier than Linux, Follow the below steps:
Step 1: Once you download the Tor file from the website you just need to go to your downloads location and then navigate to your downloaded file that will look like "torbrowser-install-win64-10.0.18_en-US.exe" so just double click on that to launch the installer.
![]()
Step 2: Now you need to select the language according to your wish and click on the OK
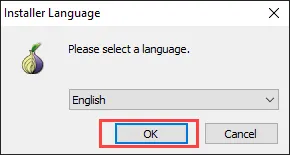
Step 3: Now the installer will ask you to specify the location where you want to set up Tor Browser, You can click on Browse for your desired path else you can go with default by clicking on Install.
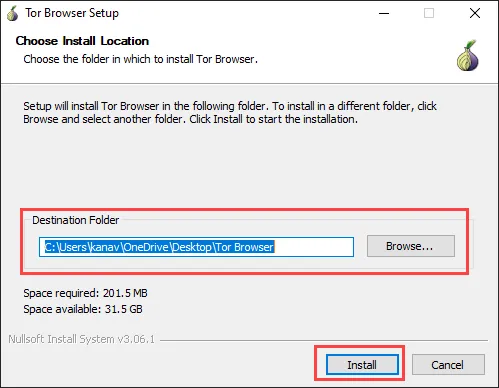
Step 4: After few seconds you will see installation is finished, Now you can click on Finish to Launch the Tor Browser.
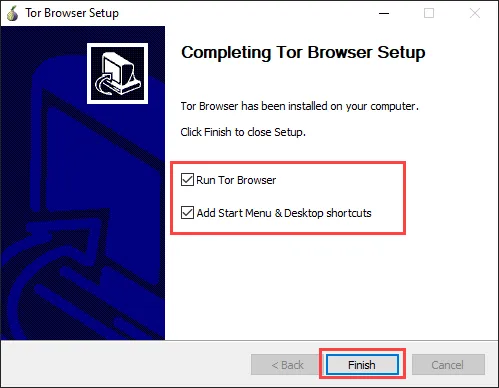
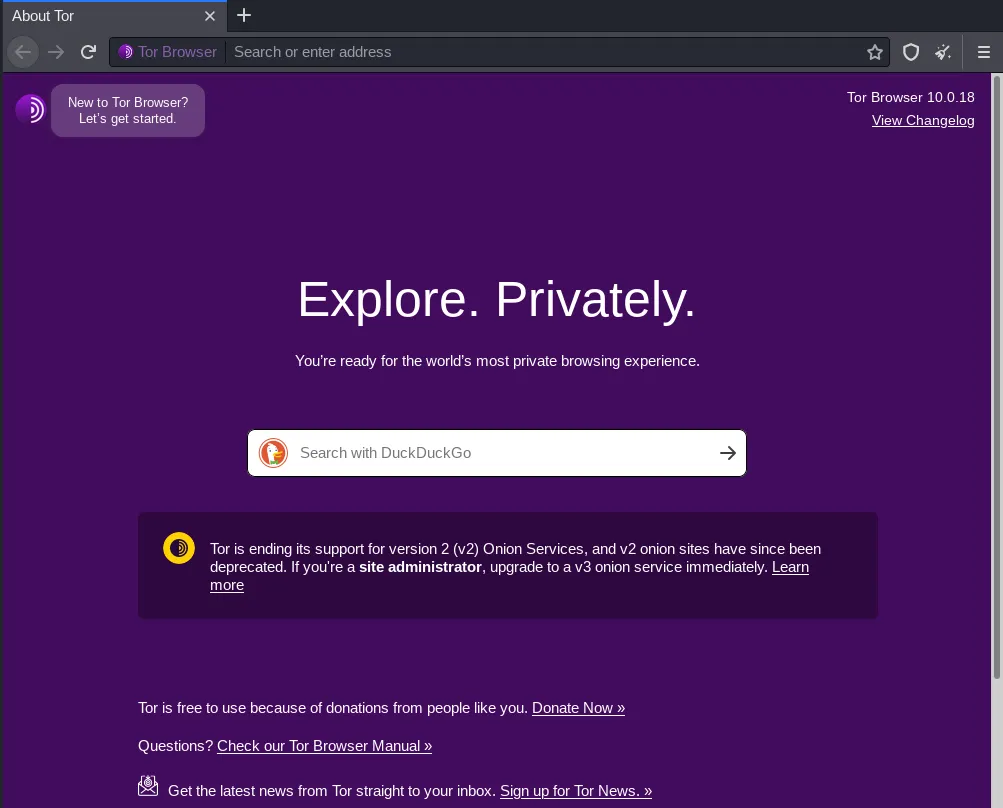
Step 5: Within few seconds it will connect you with the Tor network and you will be able to see the below screen of Tor Browser.
How to Use Tor Browser?
Tor browser came with many features and using them in Tor browser is not a difficult task, you just need to launch Tor Browser and search for anything you want.
In the below example, I am visiting my own website to show you the usage.
Step 1: Launch your Tor Browser and search techofide.com (You can go for any other website if you want)
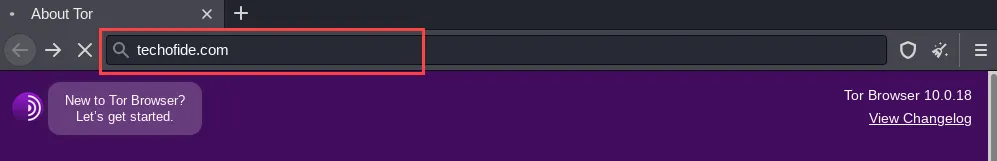
Step 2: Click on the Lock icon to check the layers from which you came to your desired website. Now in the below image, you can see our request first passes from Germany, then it passes from Switzerland and at the end, it passes from the United States and reached to techofide.com
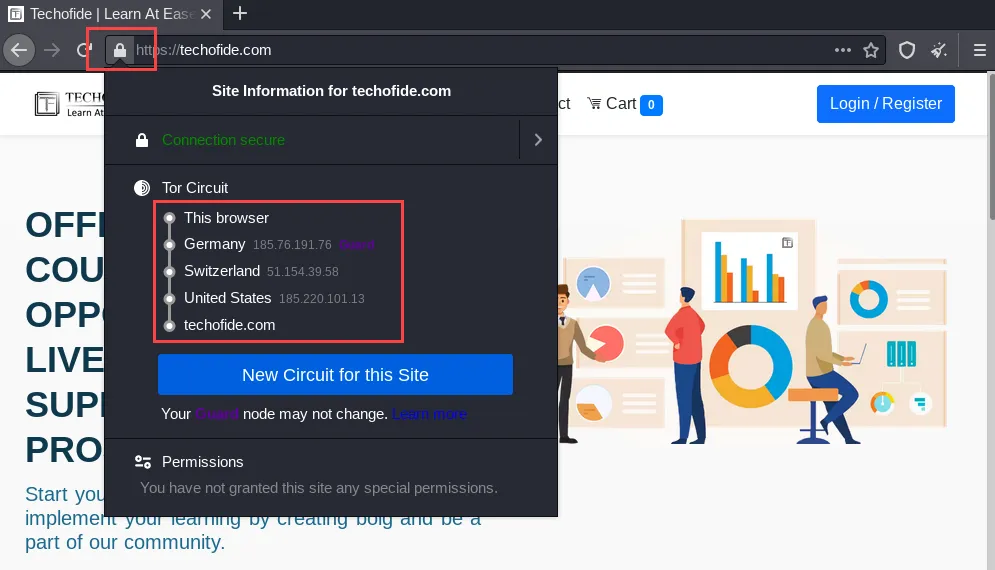
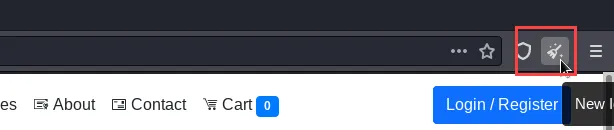
Step 3: If you want to change your Identity again, you can click on a new identity. It will close your Tor Browser and reconnect you with the Tor network. Check the below image for reference. You can also click on New Circuit for this Site to do so. check the previous screenshot.
How Does Tor Work?
When you use the Tor browser it will connect you to the Tor network to route your all web traffic that provides you anonymity.
Now you may think what is the Tor network?
Tor network is made up of a three-layer proxy like multiple layers present in Onion that's why its logo represents Onion. Tor is running by various volunteers that are present in different regions, the role of that volunteer is to provide a node (computers) that helps to pass traffic and help to build a Tor network. This is also called setting tor relays. You can also set your own relay to connecting your system with the Tor network as a node.
Let's understand the working of Tor Network with an example, Let's suppose you want to visit youtube.com so you will simply type Youtube on your browser and you will be prompted to that website but here you are directly accessing Youtube that reveals your real identity.
Now again we will search youtube.com in our Tor browser, but now it will take you to that website with another identity. Now things are looking the same but let me tell you what is the difference.
Check out the diagram of Tor Network to understand how does tor work
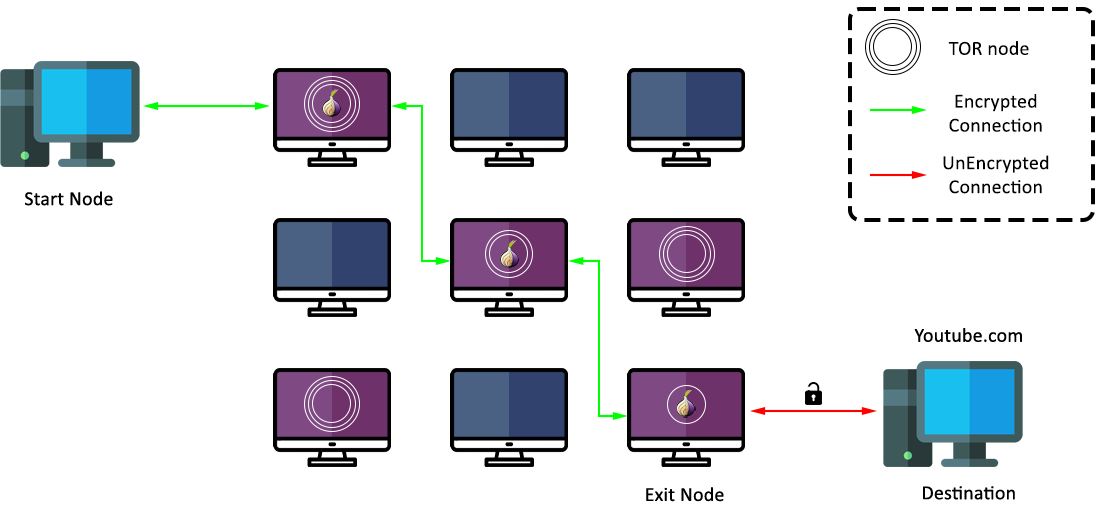
Whenever you use Tor Browser to accessing sites it will not directly hit your desired website. So if you are searching youtube.com then your request will pass through three layers, first Tor browser randomly connects to any volunteers node (Entry node) to transmit your request then it will bounce your request to randomly selected middle nodes (middle relays) and finally, it will pass your request through exit node (Third relay or layer) and then your request will reach to youtube's servers now again Youtube.com will be sent you a request as a response
So the same process again will be continued to reach your node.
Every request that passes through the Tor network is encrypted and will be decrypted at the exit node.
Hence you are passing through random nodes that will request youtube.com on your behalf and youtube thinks that request is coming from another system.
How to Safely Use Tor Browser?
There is no such app that would assure 100% protection for you from every threats or risk. You need to take care of your security with best practices. Here are few settings that I used personally to maximize the safety of tor browser:
1) Security Level
Tor Browser provides you by default three layers of security. You can check this by clicking on the shield icon present at the top right corner and then clicking on Advanced Security Settings. Check the below picture for more clarity
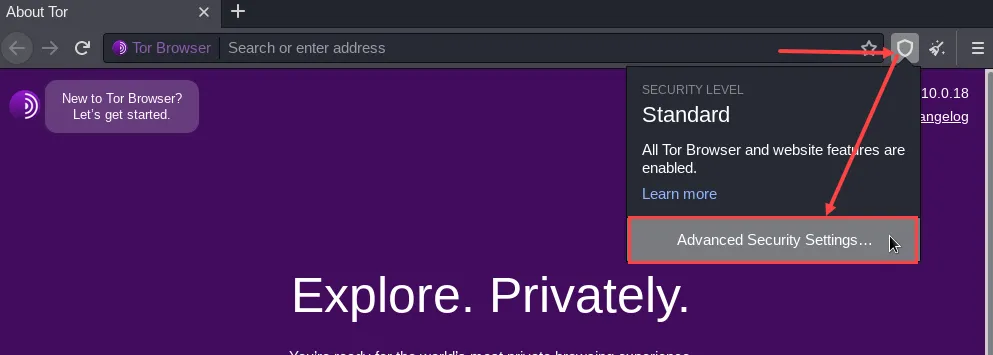
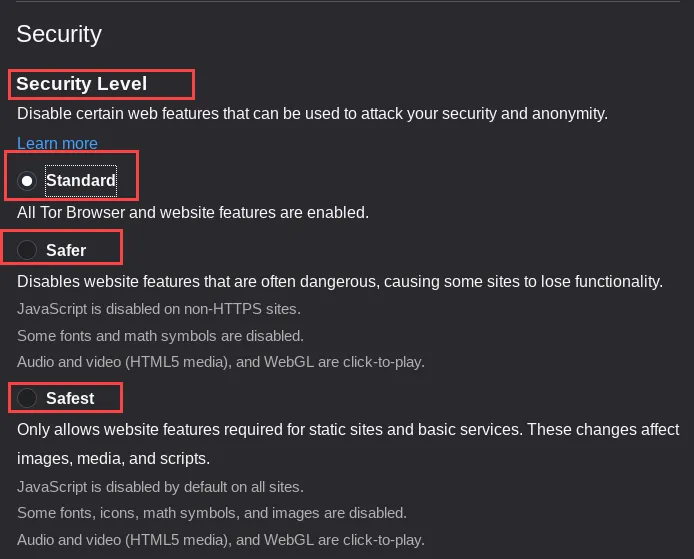
- Standard: It is just a normal mode that all browser provides you but by default, it comes with private mode.
- Safer: If you choose this option then It will disable JavaScript on insecure websites such as HTTP, It will disable some math symbols and fonts, and also prevents most video and audio by playing automatically by default to protects your privacy. It may lead to malfunction for some websites.
- Safest: A very strict and safest option that will disable JavaScript, automatic video plays, animations, images, math fonts, icons from all websites. for example, websites that contain only text will not be affected but the websites that are using Ads and a lot of animations and colourful themes may affect.
2) Advance Configuration
Whenever you try to open this option it will show you first a warning message you can open these same by entering about:config check out the below image for reference.
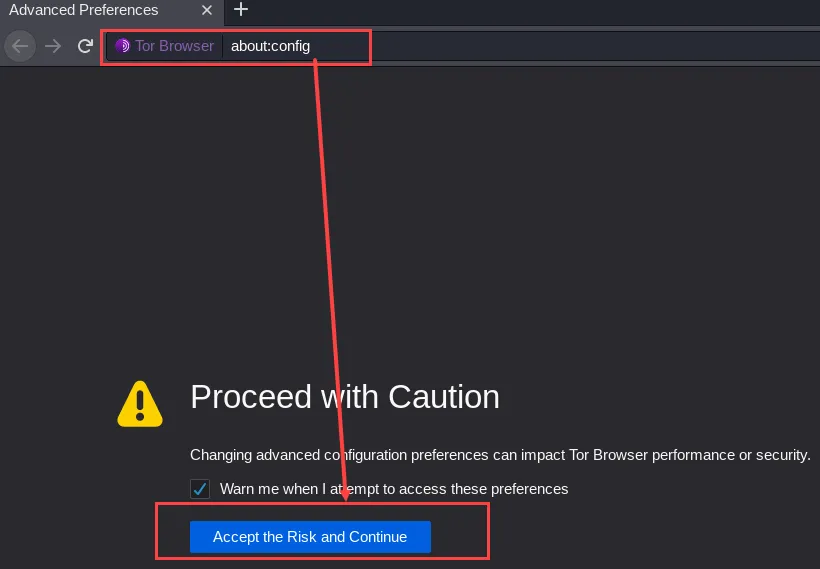
So click on Accept the risk and continue to open advance configuration.
Now we will disable some settings so follow the below steps:
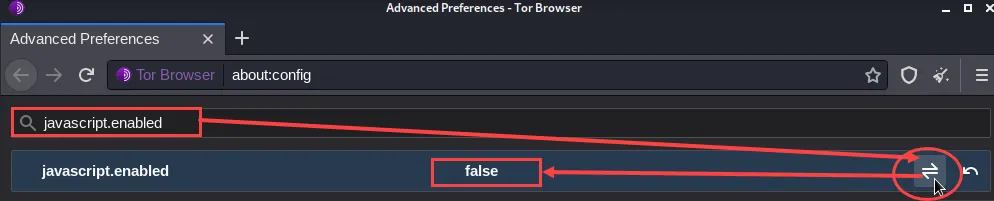
- Javascript: You need to disable JavaScript and for that search for the first javascript.enabled and make it disabled, you will see a service will appear whose value will be true and your task is to make it false by clicking on the toggle button. see the below picture,
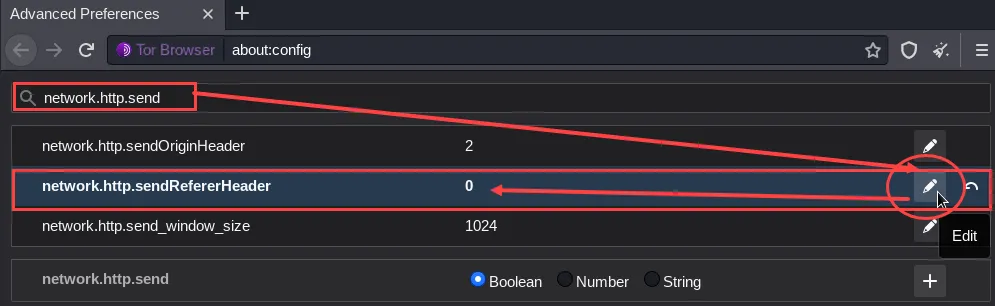
- HTTP Network: Now again we will search for one more service which is network.http.send and here we have to select network.http.sendRefererHeader and change its value from 2 to 0 by clicking on the edit icon. check the below image for reference.
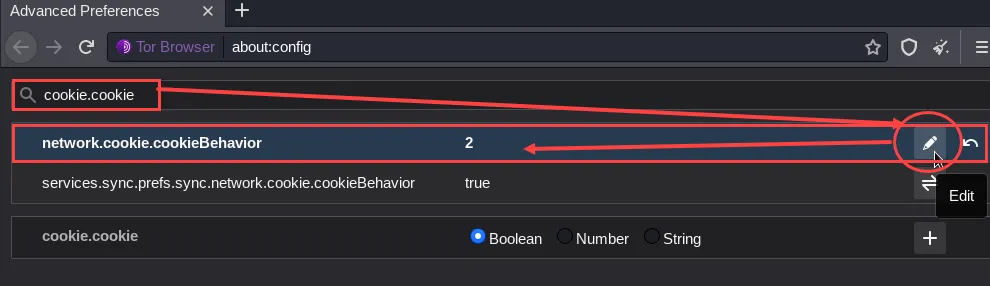
- Cookie: You need to also change the behaviour of cookies so that search cookie.cookie and select network.cookie.cookieBehavior, change its value from 1 to 2 with the help of the edit icon. See the image below
3) No Fullscreen
Don't use this browser as fullscreen because maximizing Tor Browser can allow websites to determine your monitor size, which can be used to track your activities. So using Tor on original or default size is the recommendation.
4) Up to date
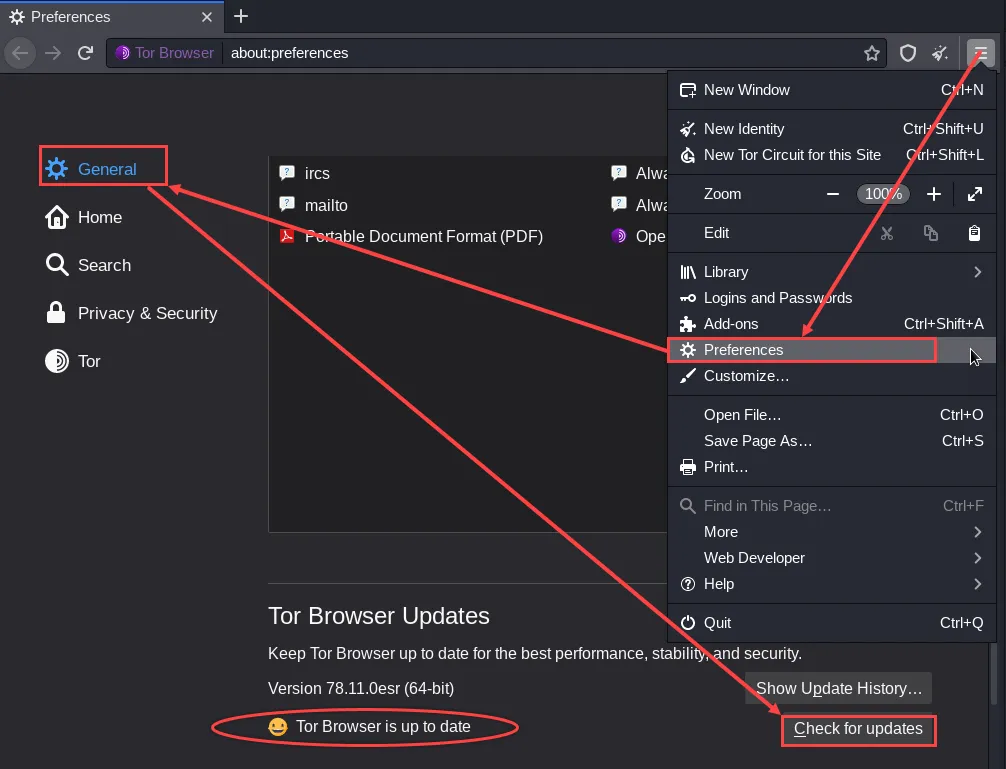
There are lots of tor's versions available but always make sure that your Tor Browser is up to date. To know how to check click on three bars located on top of the right corner then choose Preferences then under General you will see a button Check for Updates
5) Browser Add-Ons
Tor Browser is based on Firefox Hence any add-on or theme supported for firefox can be installed easily in the Tor browser.
However, the important add-ons that are working perfectly are coming by default with Tor Browser. Installing other add-ons according to your needs may lead to a serious issue that affects your security and privacy, hence your anonymity will be in danger. It is highly not recommended to install additional add-ons, and the Tor Project also not offers any support for these configurations.
Things You Should Know Before Using Tor Browser
If you are using Tor for the first time then I highly recommend you to remember the following points to know how to use tor browser:
- Do not download any torrents or media files as they required direct access to the Internet and ignore the proxy settings. Hence it can reveal our Real IP address.
- Don't enter your personal information in forums and other online forms.
- Don't try to use additional plugins because they always have your location information and it will break your anonymity for which you are using Tor. Required plugins are already installed in Tor Browser.
- Tor is only for TCP connections and it doesn't support UDP
- If the download is not recommended it doesn't mean you directly open PDF's and DOC's files online, because such document files can be embedded macros or trackers that always request internet directly and bypassing the Tor network. Hence it breaks anonymity and your real IP will be public.
- Always use the HTTPS connections to ensure the end to end data encryption with protection.
- Tor is like a door to the dark web and deep web and it is very dangerous to go for this thing without having any knowledge. I recommend you avoid such things and just focus on your work i.e, anonymity.
- DuckDuckGo is a search engine like Google, Yahoo, Bing etc. It is a default search engine because it doesn't track your browsing activities like Google and other search engines do. It always takes care of your privacy. So use DuckduckGo whenever you need to search for anything.
Is Tor Browser Safe?
The question always arises in your mind if you are using Tor the first time that Is tor browser Safe to use? or Can I use it on regular basis? So its answer totally depends on how users use that in different scenarios.
If security, privacy and anonymity during browsing is your concern then Tor is the best, reliable and safest option for you. But if you are a person who just came for the dark web and deep web then it's both yes and no.
Yes, if you have used it many times or you are well experienced in the security field and have good knowledge of dark web and deep web.
No, if you are just a beginner and just want to explore. because this is the dark side of the internet where all illegal things like child pornography, paedophiles, Drugs smuggling, Arms distribution, Live murders and much more things that you not even think are happening.
Note: In some countries like China, Germany Tor traffic is blocked. If the same thing in your country then, you need to use the bridges
Conclusion
Now we know what is tor and how to use tor browser and keep yourself anonymous, but don't think it is impossible to identify you because still, there are some possible ways to track your activity but it is very difficult. As we know exit node is the point where our data decrypt in the Tor network so at that time your data can be read by the owner of the exit relay also your ISP (Internet service provider) will identify that you are using tor. However, there are also some methods that can minimize these risks like using VPNs, VPN over Tor and Tor over VPN. As this blog is already going long so We will also discuss that in detail with practical with our upcoming blogs.
I recommend you just use tor browser to hide your browsing activities so that search engines can't track you and show you various ads and forms. Tor browser will give you a smooth and untraceable browsing experience but you might phase some issues like slow internet connection, websites uncertainty etc. as it passes from layers of different countries and block javascript.
Thanks for reading this blog please leave your comment below with an upvote.
Related Blogs
- How to Access Dark Web | Use Dark Web Links Safely
- What is Tor? | How Does it Work? | Everything About Tor Network
- How are TOR Onion Hidden Addresses Created | How Does it Work?
- Vulnerabilities in Tor | Is the Tor Browser Safe?
- How to Become an Ethical Hacker | Techofide
- How to install Kali Linux Step By Step Installation Guide
- How to make Bootable USB Flash Drive
- What is Metasploit Framework | What is Penetration Testing | How to use Metasploit
- How to Install Metasploit on Windows and Linux | [Step by Step Guide]
- What is Computer Network | Basics of Networking [With Practical Examples]