Hi Techies, this blog is very helpful and important for those who want to start their Cyber Security or Hacking field career.
The things you will see here are my years of personal experience.
In this article, I have covered all things from Scratch to Advance where we will discuss what is hacking, what is ethical hacking, how to become an ethical hacker, the responsibilities of certified hackers, career opportunities and much more.
Note: This is not just an article, this is my years of learning experience which I have shared below to help beginners. I am a CISCO and Huawei certified network administrator and working in the IT industry for the past of years in the Cyber Security and Software development field.
So let's get started from the basic terminologies.
What is Hacking?
The term "Hacking" whenever used people always think something negative like hackers, phone hack, data hack etc. But you need to understand that it is like a power that can be used in both good and bad way.
When an individual or a team successfully get access to a specific system or website without any permission of the owner is known as hacking.
What is Ethical Hacking?
As its name when a hacking operate with ethics i.e, When a hacker hacks the system under Cyber Security laws and does that for a good reason with the permission of the owner is known as Ethical hacking.
For example, Cyber Security Experts (White hat hackers), Pen- Testers, Security researchers etc. are all comes into the Ethical hacker's category.
Types of Hackers
Before understanding who are ethical hackers, let's look at the types of hackers in this world.
Black Hat Hackers
The hacker's whose intentions are bad and get unauthorized access to the systems for exploiting, spreading malicious applications, stealing data etc. Black Hat hackers have no authority and rights to access the system but they hack and theft the credential of systems and leak confidential dat a in public. They don't obey Cyber Security laws.
a in public. They don't obey Cyber Security laws.
For example Ransomware attack: This is the malicious activity performed by Black Hat Hacker's to steal data of users and companies and then ask for money.
White Hat Hackers
These hackers are also known as Ethical Hackers. They are the good guys with good intentions who always work under Cyber Security laws and do legal things. The goals of these hackers is to stop malicious activities and prevent systems from Black Hat Hackers. They are the individuals who are working for their organizations as Security Experts or Security professional.
For this, we will continue with the same example Ransomware: So when this malicious activity was happening some good guys i.e, Ethical hackers were working to capture that hacker and stop this malicious activity and after few days they stop the Ransomware and build a solution for that so that it cannot affect more systems.
Grey Hat Hackers
These are the hackers who fall on both types Black hat and White hat. They hack systems or websites the same as Black hat do but they don't have wrong intentions. They hack websites and servers by finding vulnerabilities on the system and then contact the administrator or owner of that website and tell them to fix that loopholes immediately.
administrator or owner of that website and tell them to fix that loopholes immediately.
For example, let's suppose they hack my website without my permission but then tell me that your website has a list of security issues you should have to resolve. So here he did an illegal activity by hacking my website but then they help me to make my website more secure that's why they fall on both types.
Suicide Hackers
The hackers who don't have full knowledge and use scripts of other hackers to hack websites, systems, or servers are known as suicide hackers. These hackers are considered jokers of the hacking community because they don't know rules they don't know the exact process of hacking but still hack and perform illegal activities.
There is no need for an example here because anyone who just hacks the system without any knowledge and uses others code to hack is a suici de hacker.
de hacker.
Phreaks
The hackers who use their skills only for mobile phone hacking are known as Phreaks. They only have the interest to hack mobile phones.
Who is an Ethical Hacker?
The hacker's whose only motive is to protect the systems against illegal activities are known as Ethical hacker. The hacker's that are working for the government department to protect their systems, Security experts who protect companies server or websites are the real-life examples of Ethical Hackers
How to Become a Certified Ethical Hacker?
The journey of the certified ethical hacker is very learning and practical based. It feels hard sometimes but it's really a very enjoyable and interesting field. If you want to become a certified ethical hacker then you have to know the following points:
- It is required you need CEH Certified Ethical Hacker certification
- You need to prepare for that certification.
- You need to clear an exam which is conducted by EC-Council "CEH" Certified Ethical Hacker.
- If you clear that exam you will be a certified hacker and then you can go for companies.

What Skills Required to Become an Ethical Hacker?
Now we know how to become a certified ethical hacker, but still, some of you think, like any pre-requites or skill requires to start? So my answer is you only have to know the knowledge of basic of computer, other things which I will describe below can learn side by side during preparation.
Patience
Now many of you thinking patience is not a skill and what is the relation of patience with that technical thing, but this is not only my but numbers of hackers experience that patience is the main thing which makes a person a good and successful hacker. Because Cyber Security is a field where experience grows ethical hacker also during your practicals you will face so many difficulties and errors which can be only solved by giving them time.
If you think by completing a course or even just passing the CEH exam will make you an ethical hacker and you will get lots of money and high ranked jobs then it is not true. Yes, you will be a certified ethical hacker and you also get a job but your actual journey will start from that point.
So keep learning do practicals and always calm yourself and increase your stress and patience level that will very helpful for you (My personal recommendation)
Linux
So you all know most of the practicals of hacking are performed by using Linux operating system. People use Kali, CentOS, Ubuntu, Parrot OS and lots of other platforms to practice and perform practicals of hacking.
Most of the tools which are required to perform penetration testing are works on Linux. So it is very necessary you have to know what is Linux and how to use it. If you don't know what is Linux and want to learn you can go for our well-designed course Linux Tutorials: A Complete Beginner's Course
My recommendation is to go for the above-mentioned course if you don't know about Linux.

Programming Languages
Have you ever think the tools and scripts we used to perform hacking is also made by someone? So why you are using others tools and scripts if you know how to hack? You can also create your own tools, scripts, exploits etc. But for that, you need to learn some programming languages. Most of the tools and script are build in Ruby, Python, Shell Script, C++
Also whenever any cracker needs to crack an application they use reverse engineering which is only done if you know to program.
I recommend you to start with C language as it is the Mother language from which all other languages are developed and then you can go for C++, Python, Ruby and also learn HTML, CSS, JavaScript and other web languages.

Networking Concepts
Networking plays a crucial role in ethical hacking. Because hacking is all about hacking server, hacking systems, decoding codes and getting access to anything which is on Internet, scanning machines etc. and these things includes IP addresses, ports, networking services like ssh, OpenSSL, FTP, HTTP etc. So to know these things you need to ensure that your networking fundamentals are clear.
My recommendation is you just need to know basic things about networking like what is IP, port, services, and how networking and ports are work. other things you can learn side by side during your practicals.

Command Line
We know that we will use tools, exploits, scripts to perform hacking but do you know where you will use that tools? Most of the tools are running on the shell with commands i.e, you need to open the terminal and type commands to run tools. So it is very important to make yourself familiar and friendly with the command line.
I recommend you to avoid using Windows or any GUI based things and make Linux your primary operating system and use terminal only to do anything. i.e, if you want to create a file. folder, or open an app try to do by using commands so that you know how basically Linux and commands use and you will be friendly with that soon.
Operating Systems
Good hackers are familiar with all other operating systems like Ubuntu, Kali, CentOs, Mint, Suse, BSD, Unix, Redhat, Windows, Windows Server etc. because they have used all. So you also need to use all operating system to understand what are the differences.
For example, if you need to hack a Redhat system but have not used it before then how you can hack that? that's why it is mandatory to use the different platform as much as you can.

Architectures
Whenever hacker does scanning of the system to find vulnerabilities they find from which port they can enter, how they know these things? because they know the filesystem architecture of the target operating system.
So if you want to hack any system then you have to know what is the architecture of that system and this is also very important.
I know there are lots of operating system presents and it is difficult to know about all but I am telling you almost all have the same kind of architecture. So if you want to start this I recommend you to first understand the architecture of your current system which you are using then go for others.
Database
It is another important thing that is required for every tech expert because whenever you implement something you have to save your logs and file somewhere and a secure source is a database also it is the responsibility of Security experts to save the database of the company from black hat hackers.
During any kind of disaster, a recovery process and backups help to restore computing devices and also restore data after files have been destroyed or removed. Backups of servers are important for data loss prevention, which can fully interrupt business operations. You Can create a backup of the Mysql Database by Shell script.
The database is used to store records and data of websites, mostly used databases are SQL, Postgresql, MongoDB etc...

Problem Solving Ability
Now here everything fails if you don't have the problem-solving ability. Just think a hacker knows how to hack but not able to solve any difficulty when it occurs, would you consider that person a hacker? Of course No, because hacker not only hacks he also a good problem solver.
This is the ability that normally occurs naturally in person but if you don't have this ability so don't worry you can build that just spent your time with errors and try to solve them on your own try to make different possibilities and apply them.
So if you build those skills then no one can stop you to become a good ethical hacker.
What are the Responsibilities of an Ethical Hacker?
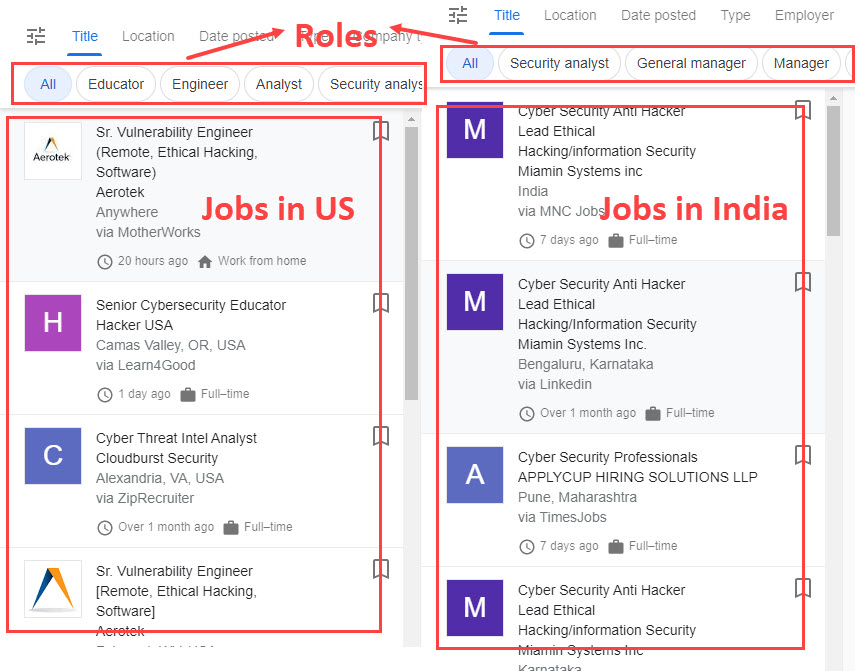
There are lots of positions of Ethical hackers. They can be Security analyst, Penetration Testers, Security Administrator, Cyber Security Auditor, IT Administrator and much more. I have discussed below in Career Options that what types of roles you will get after certified ethical hacker.
To show you how actually in real life companies mention requirements and responsibilities when they are searching for a fresher who don't have experience. I have made a template.
Below is a template that is not just an example, I have picked it from the actual companies post that was searching for System Security Engineer.
We are looking for a certified ethical hacker with the talent and confidence to perform in-depth penetration tests on our customers' computer systems. As a certified ethical hacker, you need to study the type of system used, find ways to penetrate the system and identify vulnerabilities. You may also need to generate penetration test reports and advise on security updates.
To ensure success as a certified ethical hacker, you must have advanced knowledge of computer and Internet security systems, high-level hacking skills, and the ability to produce clear and concise reports. A world-class certified ethical hacker quickly identifies vulnerabilities and provides useful tips to improve the system.
Responsibilities:
- Perform multiple penetration tests on the system
- Identification of areas with high level security. Security network review and evaluation
- Meetings with clients to discuss the current security system
- Research of the company's system, network structure and possible penetration sites
- Identification of areas with high level security.
- Reviewing and rating the security network.
- Compile penetration test reports for the customer to perform penetration tests after new security features have been implemented
- Recommend alternative updates
Requirements:
- Bachelor’s degree in information technology or computer science.
- CEH Certification.
- Good knowledge of networking systems and security software.
- In-depth knowledge of parameter manipulation, session hijacking, and cross-site scripting.
- Technical knowledge of routers, firewalls, and server systems.
- Profficency in English and communication skills.
- Good troubleshooting skills.
- Ability to find bug
Step by Step Process of Ethical Hacking
Let's see what actually a process is, which is followed by a hacker to perform ethical hacking activities. So below I have described this process in phases:
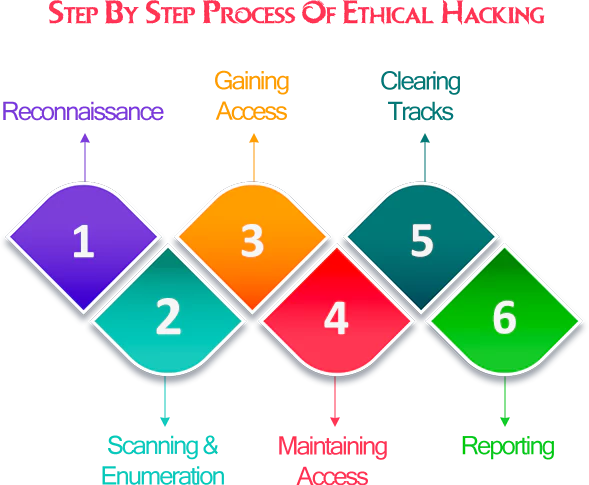
Reconnaissance
Gathering information and knowing the target systems is the first ethical hacking process. Reconnaissance is a set of techniques that are used to explore and collect confidential data about a target system. During the research, an ethical hacker tries to gather as much data as possible about a target system. They commonly used methods like footprinting, scanning, Requirement gathering etc...
Scanning & Enumeration
This is the second phase of ethical hacking where the hacker scans the targeted system to found vulnerabilities and extract all the possible data from the targeted system, the data includes username, passwords, networking ports, IP tables, routes, open service, system files and much more...
The most used techniques for that are Port scanning, Fingerprinting, Vulnurbility analysts etc. and tools that are used for those techniques are Nmap, Angry IP Scanner, Autoscan, P0f etc.
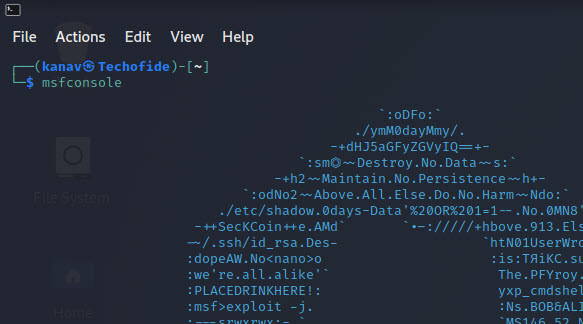
Gaining Access
This is the third phase whose goal is to grep enough information that can help to gain access to the target system.
So after finding a vulnerability you attempt to exploit it to enter into the target system. The mainly used tool in this process is Metasploit Framework. It is the tool that helps you to gain access and lets you enter into the targeted system with help of its modules (exploits, auxiliary, payloads etc...)
Want to know more about Metasploit and its usage click on Metasploit
Maintaining Access
Now in the fourth phase after getting access into the target system hackers install malicious backdoors inside that system so that next time they can simply enter into that system. Lots of tools are available to do that like Metasploit, Fat Rat, Veil, Ghost etc...
Clearing Traks
This is the stage where the hacker deletes all the log files that are related to the whole process he did so that he will not catch by anyone. This includes clearing the events to log file, var files and history of the targeted system.
Reporting
The last phase of ethical hacking is making a report where the hacker compiles all data of the targeted system and measures the success rate according to the usage of the tools. This consists of weaknesses, effective tools, data and loopholes etc...
Career Options in Ethical Hacking
With the rise of computer hacking, government organizations, financial institutions and reputable companies are recruiting qualified and ethical hackers to keep your information safe. There is no shortage of ethical hacking jobs.
According to the New York Times reports, the demand for information security personnel will result in an estimated 3.5 million vacancies created worldwide by 2021. The sector will grow by 350% by 2021.
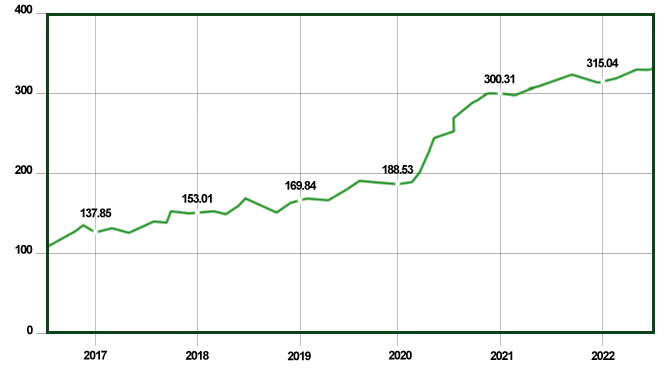
In India, the scope is expected to increase by 77,000 over the next five years. Technical hackers can search for leading companies such as Dell, Google, Wipro, Reliance, Infosys and IBM to achieve the highest-paid ethical piracy jobs in India and other countries.
However, an ethical hacker must have a legitimate bachelor's degree in information technology or an advanced diploma in network security.
Ethical Hacker Jobs
A candidate who possesses the required skills and educational qualifications can pursue any of the following positions:

1. Cyber Security Analyst
Average Base Salary: ₹529k /year
A cybersecurity analyst works with IT professionals to review the company's security measures and controls. They are responsible for planning, implementing, and evaluating network solutions by identifying system infrastructure and vulnerability prior to an attack. In addition, they will carry out various security assessment and risk analysis tests to ensure information security. Companies hire security analysts to prevent violations and cyber-attacks, helping them maintain their financial health and brand image. Because professionals have sufficient knowledge of security procedures, they protect the company from future failures and intrusions.
2. Penetration Tester
Average Base Salary: ₹603K/year
A pen-tester have to test various IT system to identify flaws. They perform various tests to identify the potential vulnerabilities and improper configuration by hacking into the network system and computers. They are also responsible for keeping a record of their activities and discovered vulnerabilities.
3. Network Security Engineer
Average Base Salary: ₹532k /year
A network security engineer is responsible for maintaining the security of multiple network systems in an organization. Keeps the system security in the development of possible plans for the system to return to normal even after problems caused by hackers, attacks, natural disasters or other means.
4. Information Security Officer
Average Base Salary: ₹1228k /year
An information security officer is the top manager of an organization responsible for maintaining the business strategy. Implement strategies to ensure the security of information and technology assets Helps organisational staff develop, implement, and maintain procedures that help reduce information leaks.
5. Data Security Analyst
Average Base Salary: ₹491k /year
Data security specialists or analysts are responsible for planning and performing data protection on the company's computers and networks. They work closely with the organization's staff to educate them about safety protocols.
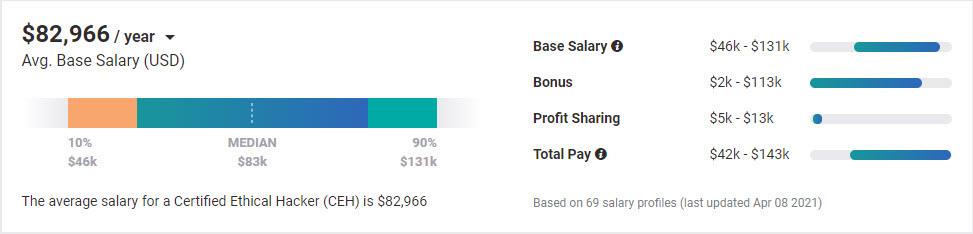
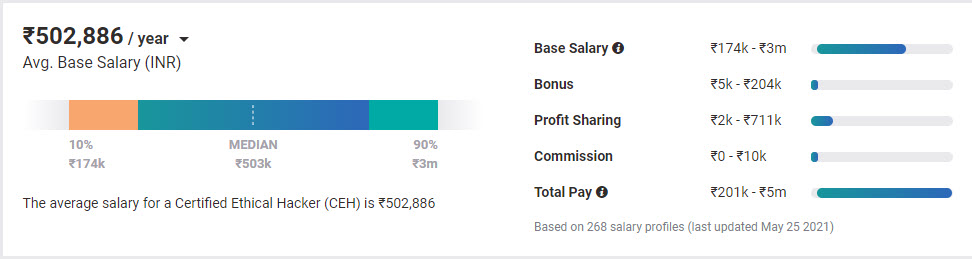
Ethical Hacker Salary
Certified ethical hackers, according to Payscale, have an average annual income of $82,966. The average starting salary for a certified ethical hacker is $97,000, according to Steven Graham, Senior Director EC-Council. NowiresSecurity founder Eric Geier estimates more conservative from $50,000 to $100,000 per year in the first years of work, depending on your employer, experience and training. Those with several years of experience can earn $120,000 or more per year, especially those who work as independent consultants.
How to Learn Hacking to Become an Ethical Hacker?
There are lots of opportunities present in the market to start learning ethical hacking, various websites offering online courses, offline institutes and the Internet is the biggest source of grepping knowledge. But the main problem is good courses are a bit costly that can not be afforded by beginner's and students and on the other side free content is available in an unstructured way and also it is lots of content that make so difficult to choose from where to start, what to learn and what to not?
So if you are a beginner and want to start learning then it is a good approach that you first go to the Internet and explore according to your job role like on which sector you are looking for and what are the requirements for that and then learn according to that topic with videos. So later when you think it is enough you are ready to give an exam of CEH then you can join the institute for a month to polish your skills and to learn the exam patterns and tips.
My Recommendations
So I can share some tips or strategy with you which helps you to fulfil your dream with the right path. The points I am mentioning below are applicable to beginners, intermediate and advanced level.
1. Make yourself comfortable with Linux and its command line. If you don't know Linux then you can start learning Linux by clicking on Linux Tutorials: A Complete Beginner's Course
2. Try to learn programming languages like C, C++, Python, Ruby. If you don't know the programing language then I recommend you start from the C language and If you know then go for Python and Ruby.
3. Try to explore tools that are used in ethical hacking like Nmap, FatRat, Metasploit, Recon etc.
4. Create your own dummy website and keep the practice on that with tools and learn HTML, JavaScipt and other website languages.
5. Join Ethical hacking groups from social media so that if you stuck at anything during practicals so you can get help from others. I also have a Group Ethical Hackers | NetHunter for beginners where you can learn other stuff related to your hacking career.
6. Try to read documentations of tools that will help you to understand the usability of tools in more depth.
7. Always update yourself with the official EC-Council website to know what new things are happening there because they mostly launch events and scholarship programs that will help you in your certification exams.
8. Try to explore the internet as much as you can and learn everything if you get the chance or found anything whether it is related to your field or not because no one knows when those things will help you.
9. Keep learning every day don't assume you know all because a good hacker always keeps learning.
10. The most important point is getting certified is good but also costly so don't worry if you can't afford it because certifications are not mandatory you can also start without that and grow yourself.
If you want to learn with me then it is very easy and free for you, I always create blogs and videos related to cybersecurity and ethical hacking from scratch to advance so you can follow my blogs and videos.
I regularly post new blogs or videos to check them click on Blogs and Videos
Conclusion
I have tried to cover almost everything that new beginners required to know the right path to become an Ethical Hacker to start their ethical hacking career. I hope you like this blog and I have also started a series for those who want to learn ethical hacking, if you also want to learn hacking with me you can follow my blogs and videos
To start your first step you can read my blog on Metasploit Framework
If you found this blog helpful then please don't forget to give your comment below as a feedback
Below is one practical video for you to learn ethical hacking
Related Blogs
- What is Metasploit Framework | What is Penetration Testing | How to use Metasploit
- How to Install Kali Linux [Step by Step Installation Guide]
- How to Install Metasploit on Windows and Linux | [Step by Step Guide]
- What is Smurf Attack? | What is the Denial of Service Attack? | Practical DDoS Attack Step By Step Guide
- What is DoS Attack | How to do Denial of Service Attack [Practical Demo]