This is the blog where you will see one of the most famous and powerful tool for password cracking which is John the Ripper.
John the Ripper is the tool that is used by most of the ethical hackers to perform dictionary attacks for password cracking. In this blog, I have shown what is John the Ripper, How to use John the Ripper, How John the Ripper password cracker works and practical tutorial on John the Ripper usage.
So Let's get started...
What is John the Ripper?
John the Ripper is the name of the password cracker tool that is developed by Openwall. As the name, It is used to crack password hashes by using its most popular inbuilt program, rules and codes that are also an individual password cracker itself in a single package.
It automatically detects types of password hashes, you can also customize this tool according to your wish. It can be used to crack password-protected compressed files like Zip, Rar, Doc, pdf etc.

What is a Hash Function?
Hashing is the process of converting an input of any length into a fixed-size string of text using the mathematical function (Hash Function) i.e, any text no matter how long it is can be converted into any random combination of numbers and alphabets through an algorithm
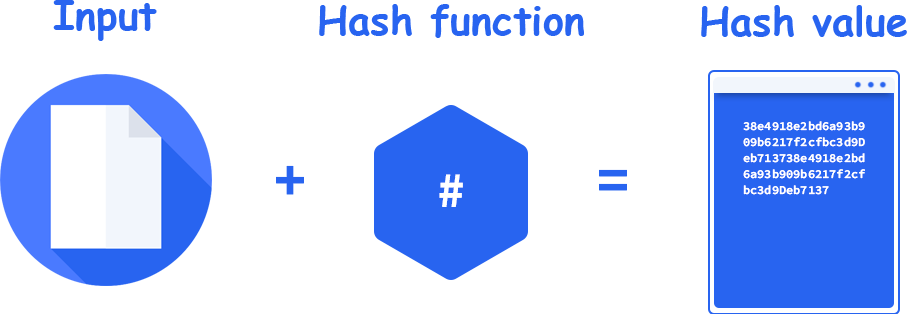
- A message to be hashed is called input
- The algorithm that encrypts string into hash is the so-called hash function
- The output called the hash value
There are many formulas that can be used to hash a message
Hash Function Example
Let's understand hashing process with a real-life example. The best example is how our system password stores in the database.
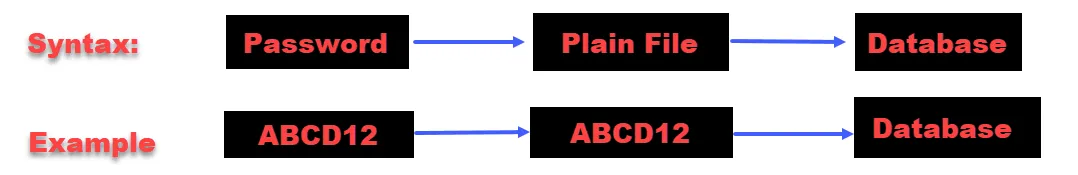
Without Hashing Algorithm
Whenever you set a password it will directly store in the database as a text file that may be read easily if the system compromised. It will save your password in a plain file as the same string you entered. Check the below image with syntax and example
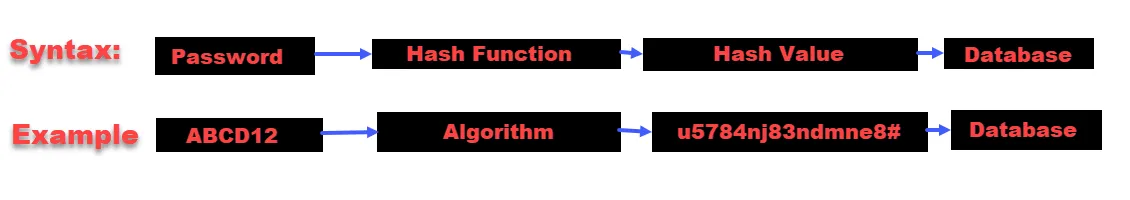
With Hashing Algorithm
Whenever you set your password it will take your password as an input string and with the help of hashing function, it converts that password into a hash (random combination of number and alphabet) and stores it in the database. It enhances security by encrypting input strings. It will save your password in a different format so no one can read it even if your system compromise.
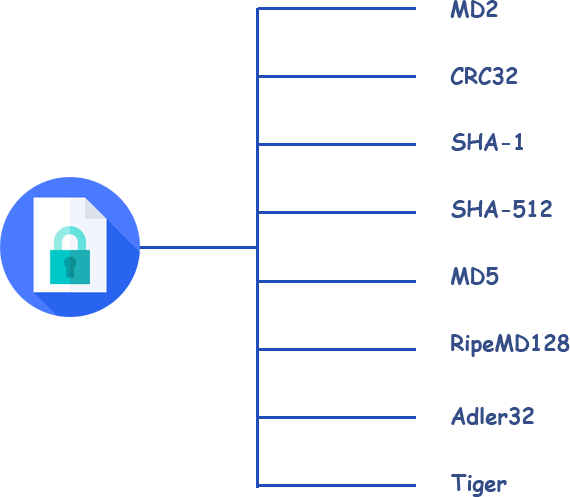
Types of Hashing Algorithms
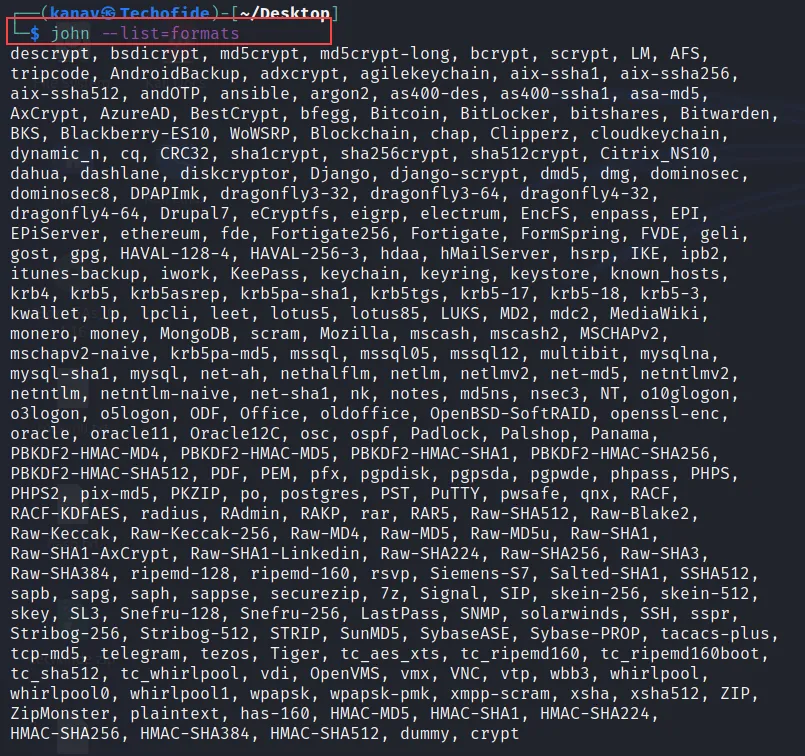
John the Ripper tool are able to perform various attacks and crack a lot of hash formats such as MD5, SHA1, Adler32, SHA512, MD2 etc.
You can check all the formats that supports by JTR with the following command
john --list=formats
How John the Ripper Password Cracker Tool Works?
The main objective of John the Ripper is to crack the password. There are many ways that can be supported but it is mainly known for Dictionary attacks. However, you can also run other types of attacks like Bruteforce attack, Rainbow Table etc.
Dictionary attack: This is the popular and most usable attack in the JTR (John the Ripper) password cracker tool where we used pre-defined words or a list of words that can be used to crack the password. This attack uses the words from the wordlist (A text file having pre-defined words) and matches every single word from the list with a password to crack in sequence.
Que: Do you know why it's called Dictionary attack?
Ans: This attack uses pre-defined words that are present in english dictionary, Hence its name is dictionary attack.
Brute-force attack: If you are using this attack then you have to do the configuration of few things before its use such as the defining minimum and maximum lengths of the password, defining possible characters that you want to test during the cracking process like (special characters, alphabets and numbers).
For Example, The matching string that you are using for cracking passwords should include uppercase alphabets, special characters and numbers like ABC32@$
The user gets a password on the successful match, but this effective process is slow. for example, a 10-character password including upper and lower letters along with numbers and special characters will take over 10 years to be guessed by a computer,
John the Ripper Download
It was developed for Unix Operating systems and was only work on Linux based systems but now available for all platforms such as Windows, BSD, Mac.
In Kali Linux John the Ripper is `already available under password cracking metapackages, so you don't need to download it. If you don't know about Kali Linux and want to install that then you can click on how to install Kali Linux
- You can download John the Ripper password cracker from the official website Openwall.
- You can also get the source code and binaries according to your operating system,
- You can contribute if you like this tool on GitHub
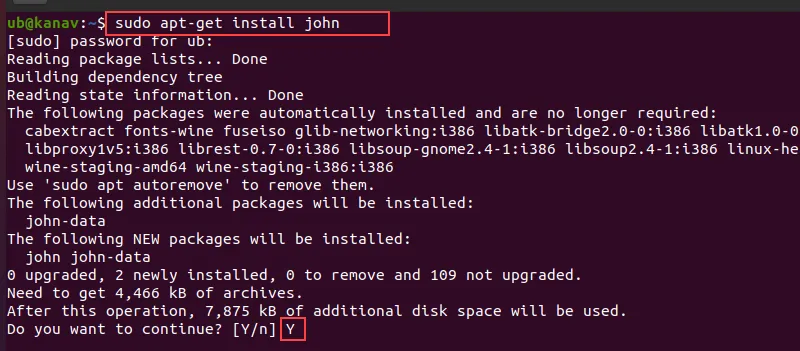
How to Install John the Ripper Password Cracker?
As I told it already present in Kali Linux that can be executed by opening the terminal and running the john command. Installing JTR binaries on other systems are also easy.
If you are using different Linux distributions like Ubuntu, Fedora, Arch etc. then you can install it by running the below single command the difference in command only will be the package manager i.e, for Ubuntu you use apt, Arch uses Pacman and Redhat uses yum. So replace your desired package manager name in the below command according to your device.
sudo apt-get install john
What is John the Ripper Used for?
The penetration testers, ethical hackers, security experts and other Cyber Security professionals use this tool to find weak algorithms and then make them strong so that they can't be hacked.
- Security professionals build their confidential files with a strong hash algorithm to prevent external unauthorized access.
- Hackers used it to crack multiple accounts and simply crack their credentials.
- Security experts use it to strengthen their encryption.
- It can also be used for hacking shells and passwords
- SHA-crypt hashes
- It provides a mangling feature which is a preprocessor in JTR that optimizes the word list to make the password cracking process faster.
How to Use John the Ripper
Now we have enough knowledge of the John the Ripper tool and we also installed it. Let's see how we use it.
Using this password cracker tool is very easy and straightforward, you just need to type john followed by the hash file that you want to crack and then just define the format of the hash and hit enter.
john hash.txt --format=RAW-MD5
In the above picture, you can see lots of supported formats, You can do various things with this tool such as using wordlists, rules, modes, options, decrypting formats etc, We will see below how to use these various things in this tool.
John the Ripper Tutorial
Now in this section, we will learn practically how to use john the ripper password cracker to crack password-protected zip, rar, hash, MD5 and SHA1 files, also we will see how to crack Linux passwords of all users.
Note: In this tutorial, we will also use some basic Linux commands to create text files and redirect their outputs to other files. So if you are not familiar with the command line then you can check my blog by clicking on basic Linux commands.
So Let's get started...
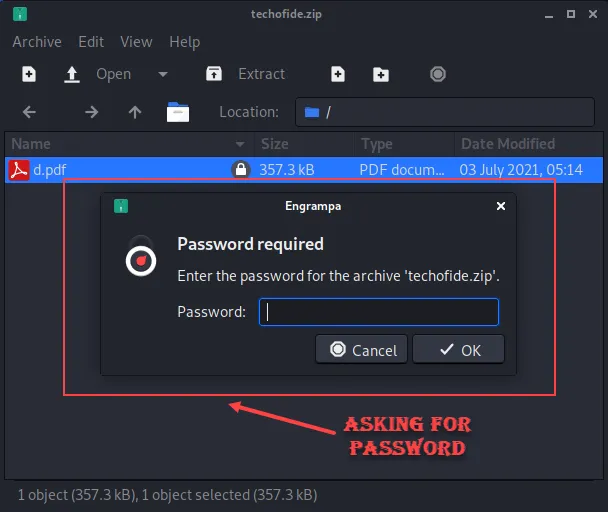
1) Cracking Zip File
Step 1) Now you can see that we have a zip file techofide.zip which is password protected and asking for a password to open it
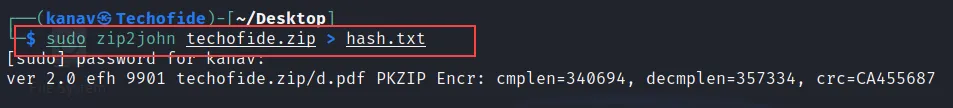
Step 2) Now as we know JTR use hash to crack password, so we first need to generate a hash of our zip file. The below command will generate a hash of our techofide.zip file and store that generated hash value into a hash.txt file
sudo zip2john techofide.zip > hash.txt
Step 3) Let's break it with our tool, So now we have a hash of our zip file that we will use to crack the password. In the below command we use the format option to specify the zip file and then the hash.txt file where we store our hash value.
sudo john --format=zip hash.txt
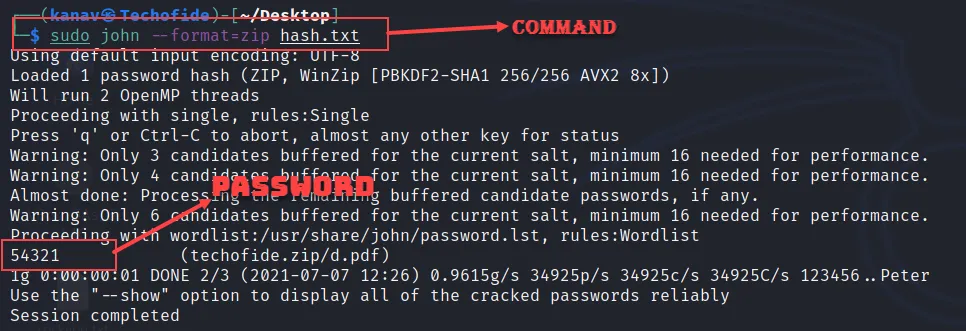
In the above picture, you can see our command complete the session and returns with the correct password 54321
You can crack the rar file with the same command just replace zip with rar.
2) Cracking MD5 Password
Step 1) In this example I am generating a hash by using md5 hash generator to show you how to crack MD5 formatted files password. In the below image you can see I have generated the hash of the 12345 string. You can copy the MD5 hash to perform the same practical
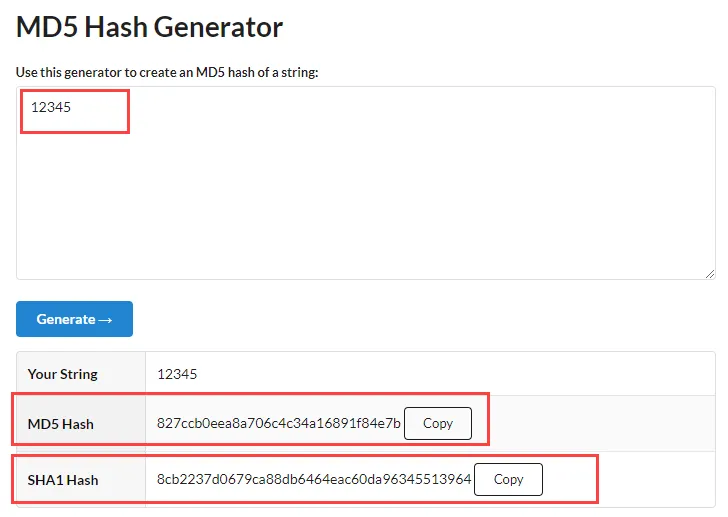
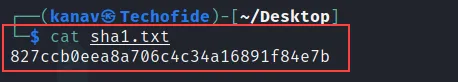
Step 2) In the below picture you can see the file sha1.txt. I have used the cat command to show you the data of the sha1.txt file, You can see the MD5 hash value 8772cc...
Step 3) Now let's crack the MD5 Hash, In the below command we have specified format along with the hash file.
john sha1.txt --format=RAW-MD5
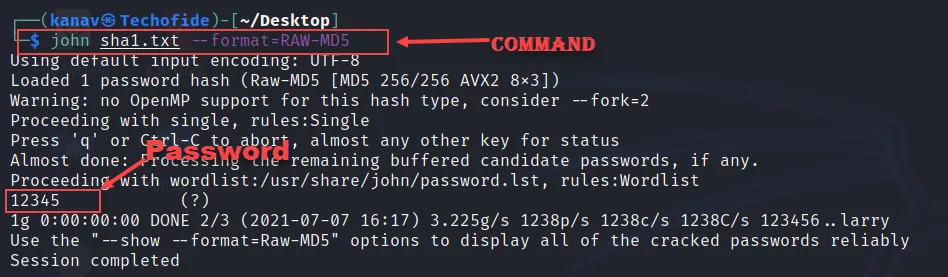
In the above screenshot, you can see the output that cracks the hash and returns the 12345 passwords.
3) Cracking SHA1 Password Using Wordlist
Step 1) Cracking SHA1 type of password is the same as MD5 you just need to replace MD5 with SHA1 but here I will also show you how you can use wordlist to perform a dictionary attack with John the Ripper to crack the password.
Note: If you are performing this attack in Kali Linux then you can find wordlists folder i.e, in /usr/share/wordlists/ location, you can see fasttrack.txt, nmap.lst and rockyou.txt. I am using the rockyou.txt file
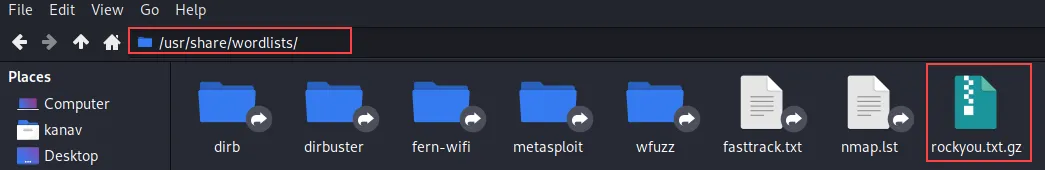
If you are using a different operating system then you can download this file by clicking on rockyou.txt
Step 2) Use the below command with your hash file to crack it.
john SHA1 rockyou.txt --format=RAW-SHA1
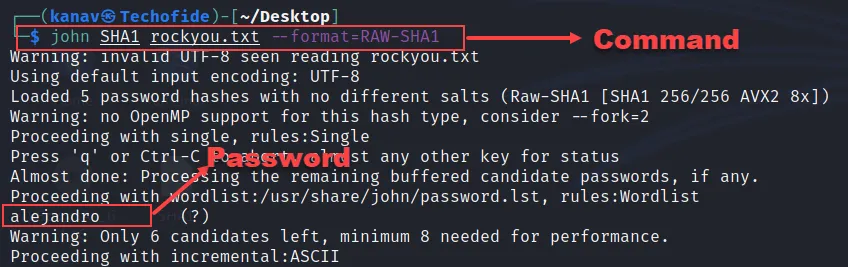
In the above picture, you can see it returns the correct password i.e, alejandro. In this command, SHA1 is our hash file and rockyou.txt is our wordlist
4) Cracking Linux Password
Step 1) When we create a password of the Linux system it stores in /etc/shadow location in encrypted form i.e, like a hash. So cracking a Linux password is easy with just a single command that is given below.
sudo john /etc/shadow
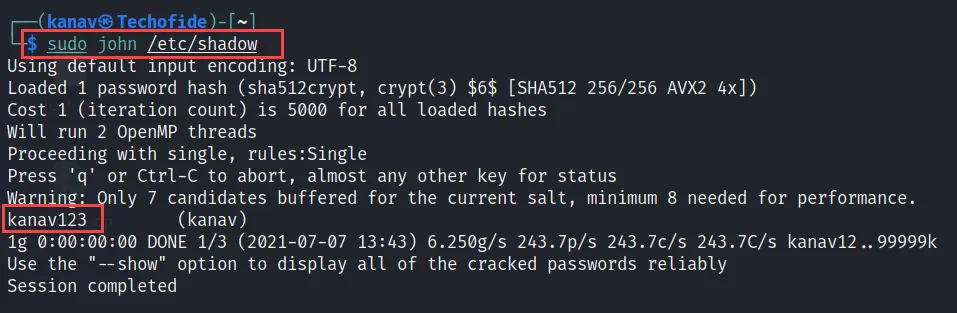
In the above image, you can see it decrypt all users passwords i.e, user Kanav's password is kanav123
Conclusion
Now we know what is John the Ripper, How to use John the Ripper, How John the Ripper password cracker works, How passwords can be cracked and also a tutorial on its real-life important uses, but this not get over yet there are lots of other things that can be done by JTR.
Remenber if the password is long it will also take long time to crack. We will see more practicals on that in our upcoming blogs.
I hope you like this blog, please like, share and drop your comment on this blog that will be a great support from you
Thanks for reading this article.
Related Blogs
- Nmap Commands | How to Use Nmap Tool
- How to Become an Ethical Hacker | Techofide
- How to Install Kali Linux Step By Step Guide
- Linux Commands | Linux Commands Cheat Sheet
- What is Metasploit Framework | What is Penetration Testing | How to use Metasploit
- How to Install Metasploit on Windows and Linux | [Step by Step Guide]
- What is Computer Network | Basics of Networking [With Practical Examples]